NetworkWhois Community
Latest articles, tutorials and insights from our networking and security experts
Recent Articles
25 total articles
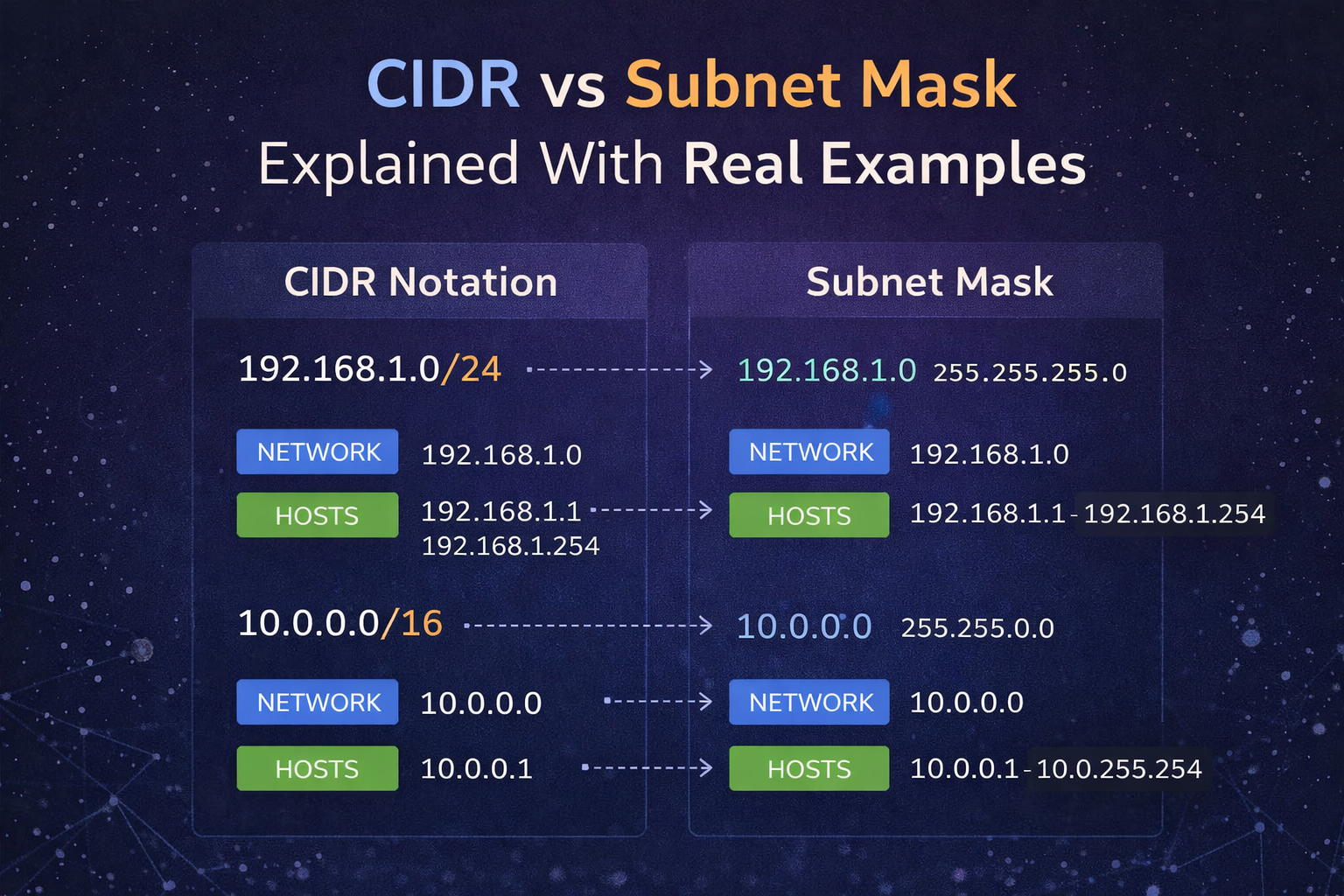
CIDR vs Subnet Mask Explained With Real Examples
CIDR and subnet masks describe the same network boundary in different formats. This guide explains how to translate between them and use them correctly in real IPv4 examples.
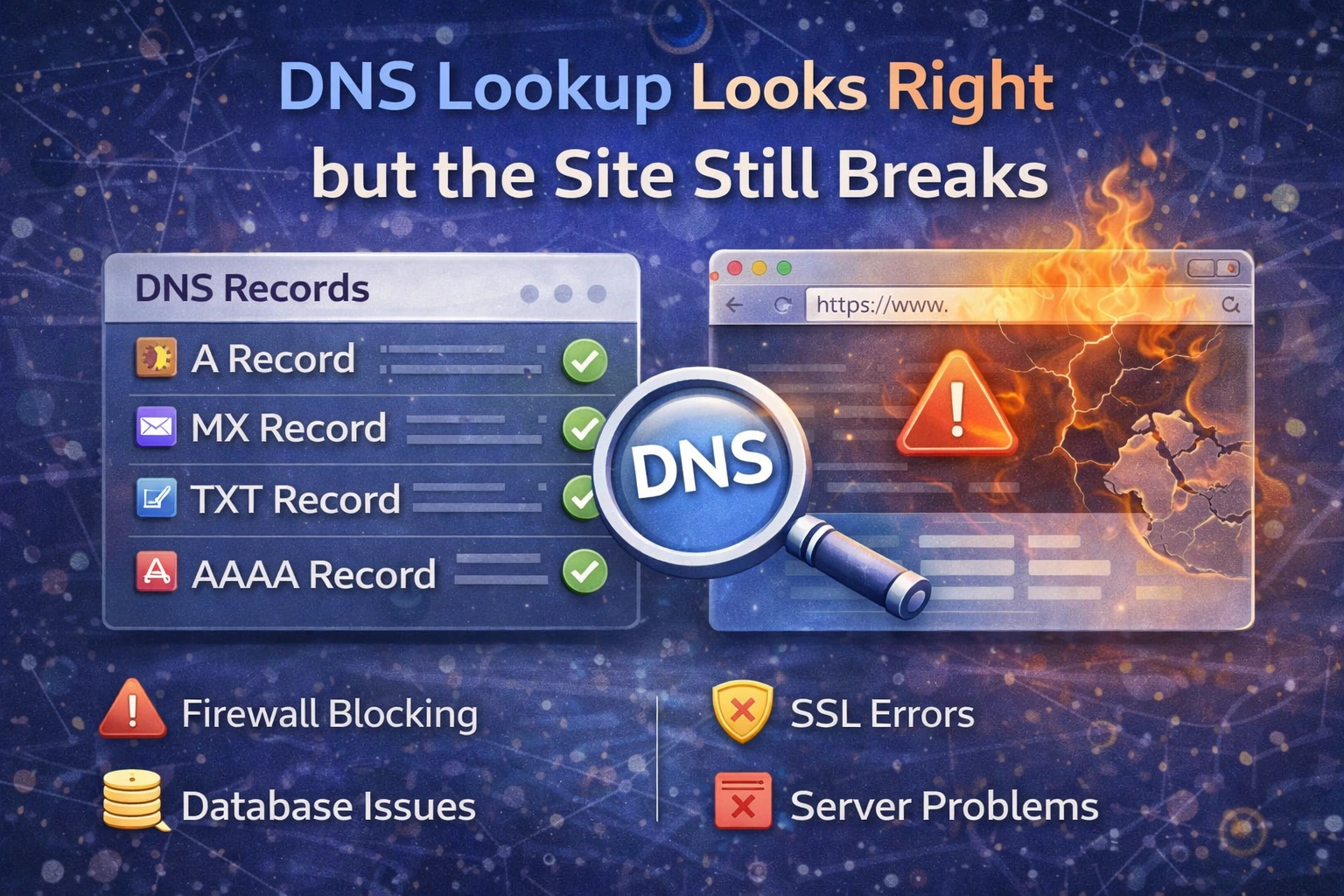
DNS Lookup Looks Right but the Site Still Breaks
Sometimes DNS records look correct but the website still fails. This guide explains what to check next, including propagation, SSL, origin reachability, IPv6, and application-side issues.
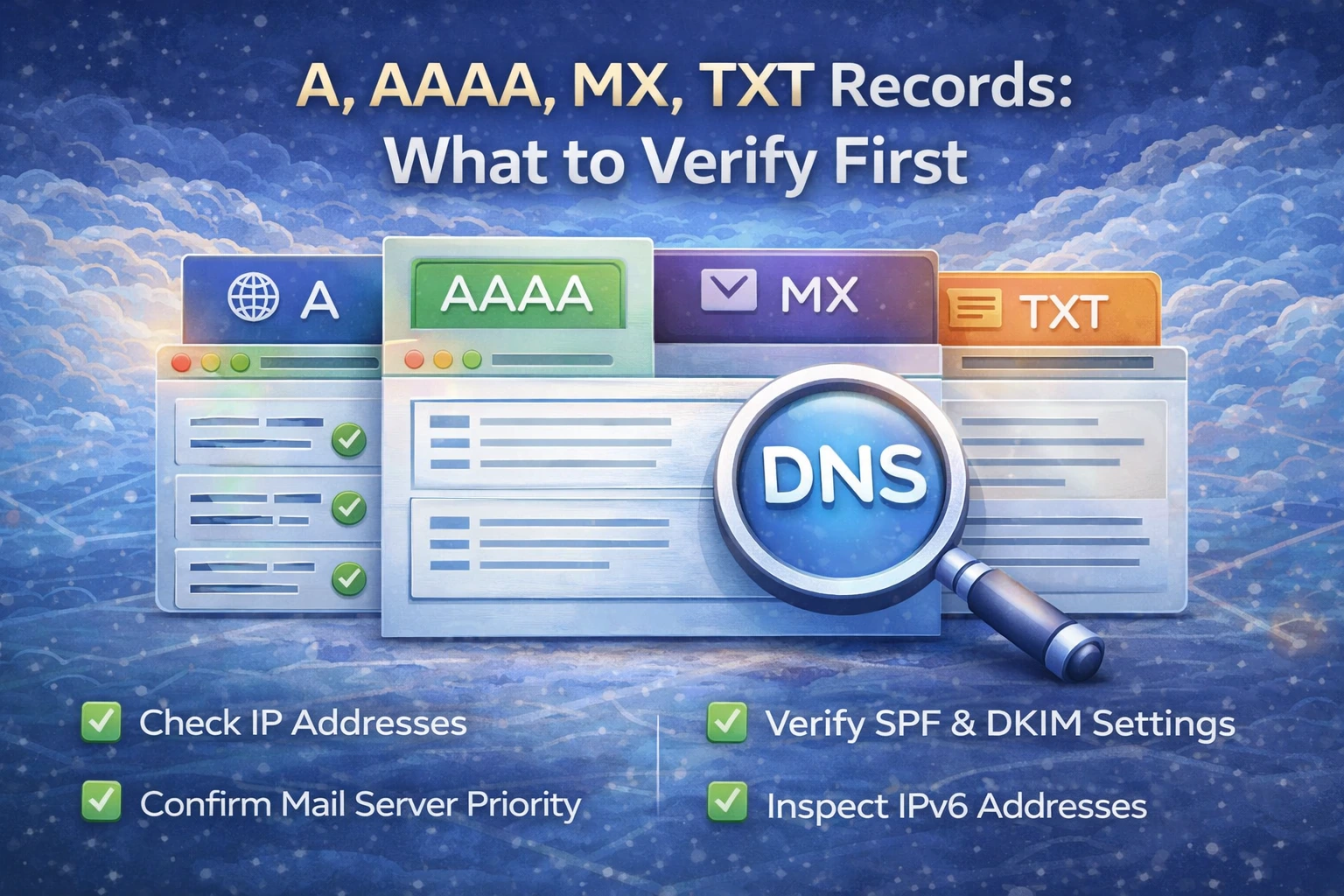
A, AAAA, MX, TXT Records: What to Verify First
When a domain is not behaving correctly, you do not need to check every DNS record at random. This guide shows the right order to verify A, AAAA, MX, and TXT records based on the problem you are seeing.
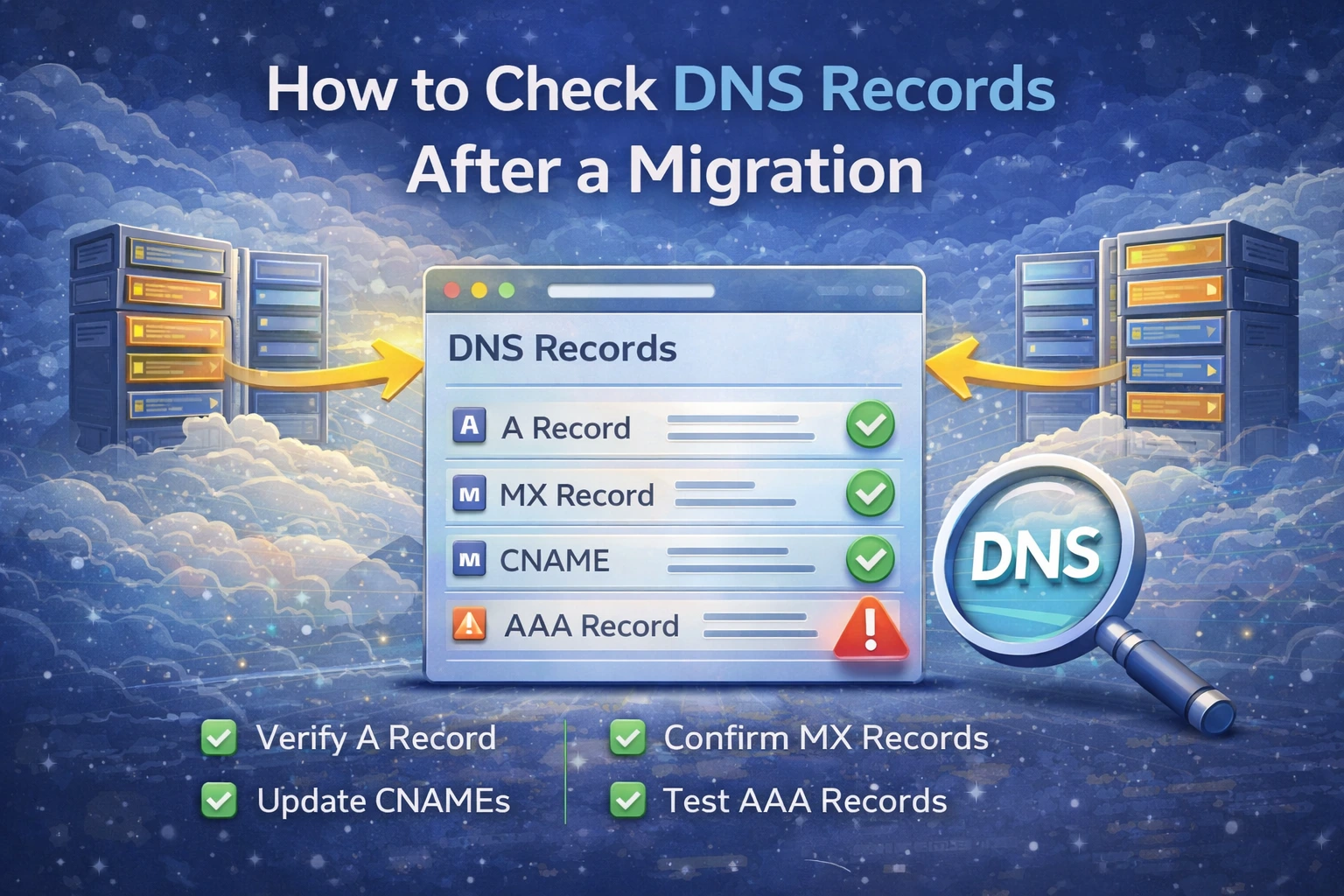
How to Check DNS Records After a Migration
After moving a website, server, or mail provider, DNS mistakes are one of the most common reasons things still fail. This guide explains what to verify first and how to confirm live DNS records after a migration.
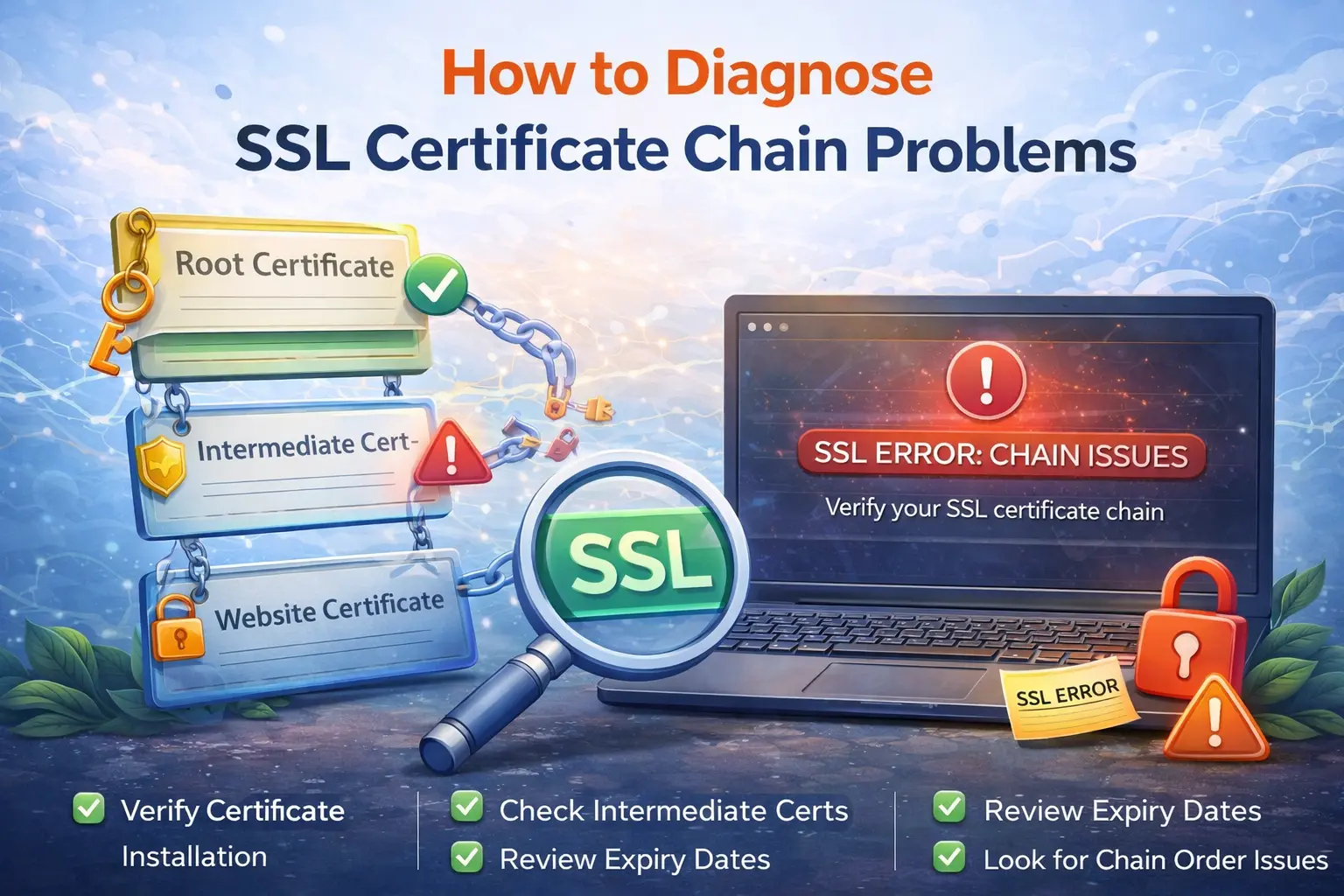
How to Diagnose SSL Certificate Chain Problems
SSL issues are not always caused by an expired certificate. This guide explains how to diagnose incomplete chains, hostname mismatches, and trust problems that affect websites, APIs, and mail services.
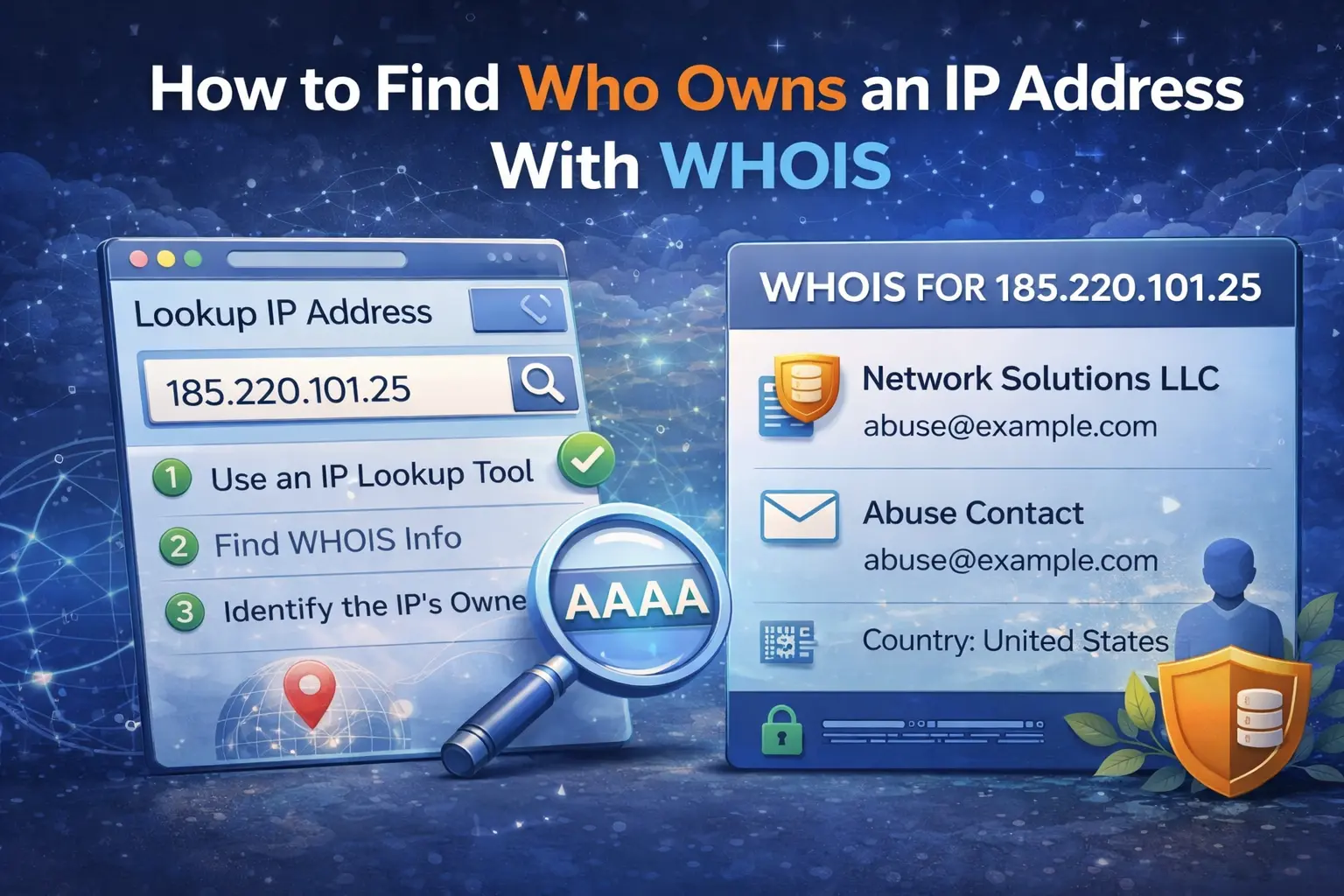
How to Find Who Owns an IP Address With WHOIS
IP WHOIS helps you identify which organization controls an IP address, understand ASN and allocation details, and decide what to investigate next when traffic looks suspicious.
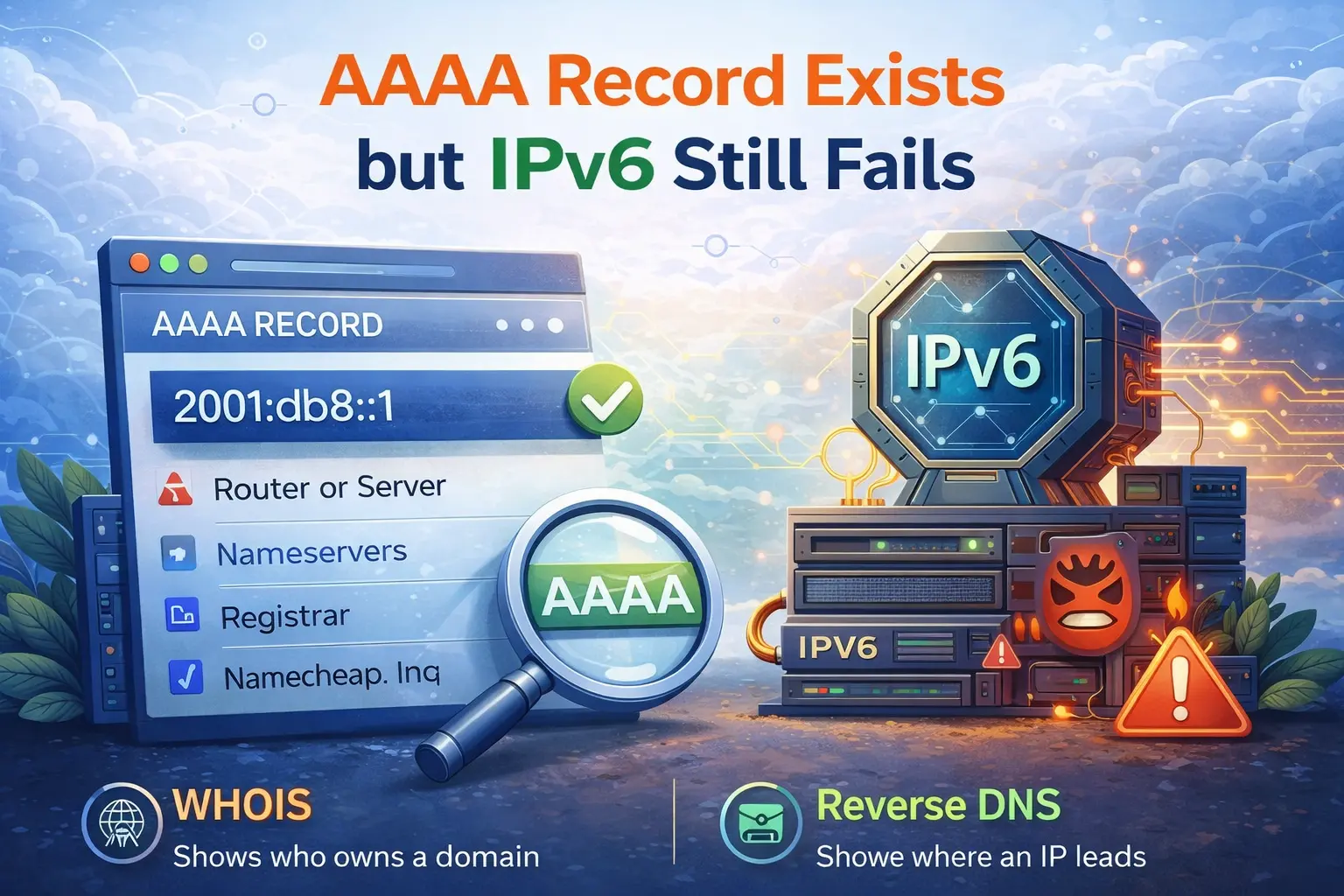
AAAA Record Exists but IPv6 Still Fails
Publishing an AAAA record is not enough to make a service reachable over IPv6. This guide explains the most common reasons IPv6 still fails, including firewall rules, routing, listener configuration, and premature DNS changes.
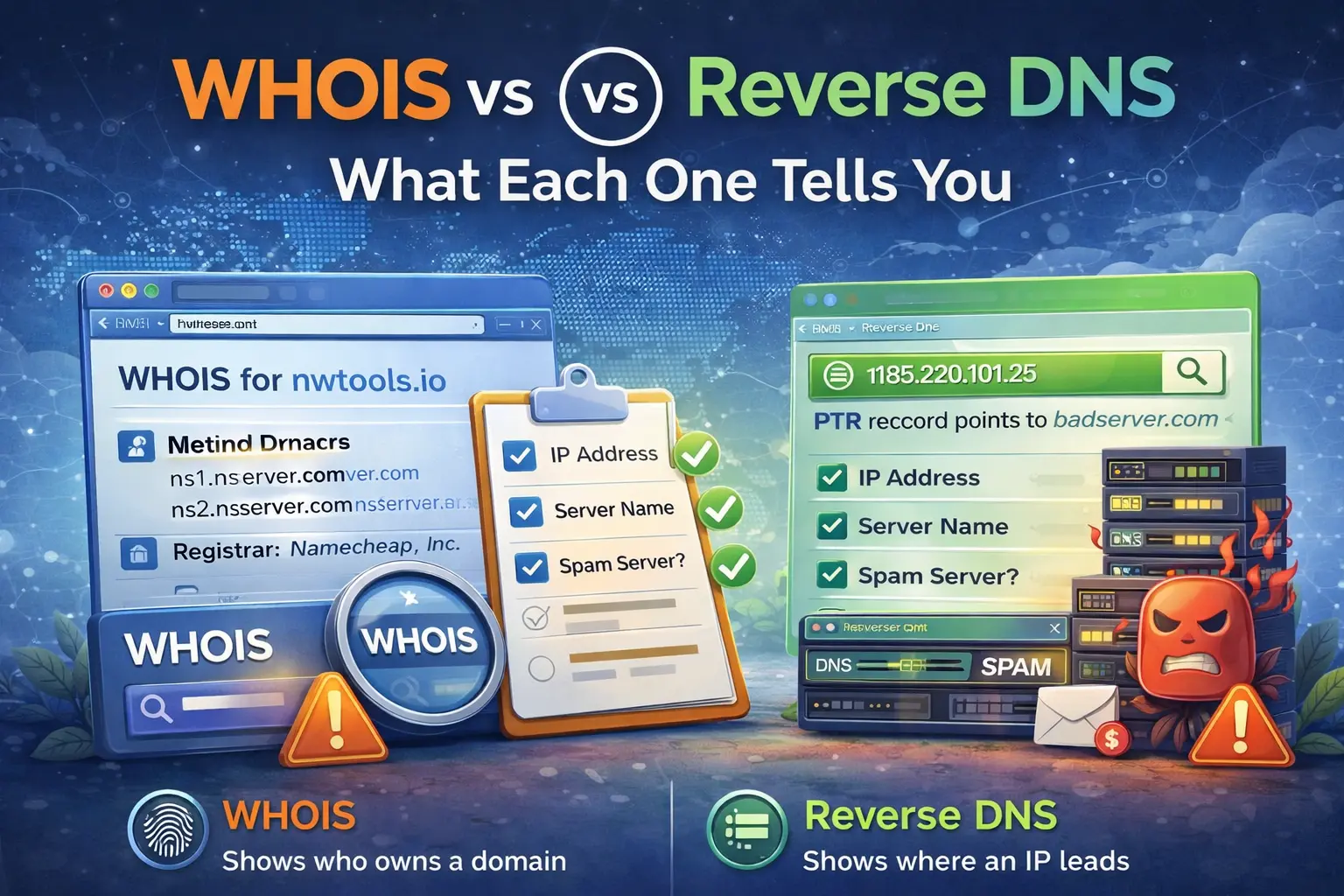
WHOIS vs Reverse DNS: What Each One Tells You
WHOIS and reverse DNS answer different questions about an IP address. This guide explains what each one reveals, when to use them together, and how they help with abuse investigation and mail troubleshooting.

Why Reverse DNS and SPF Are Both Needed for Email
SPF and reverse DNS solve different trust problems in email delivery. This guide explains why you need both, what each one proves, and how missing PTR records still hurt sending reputation.
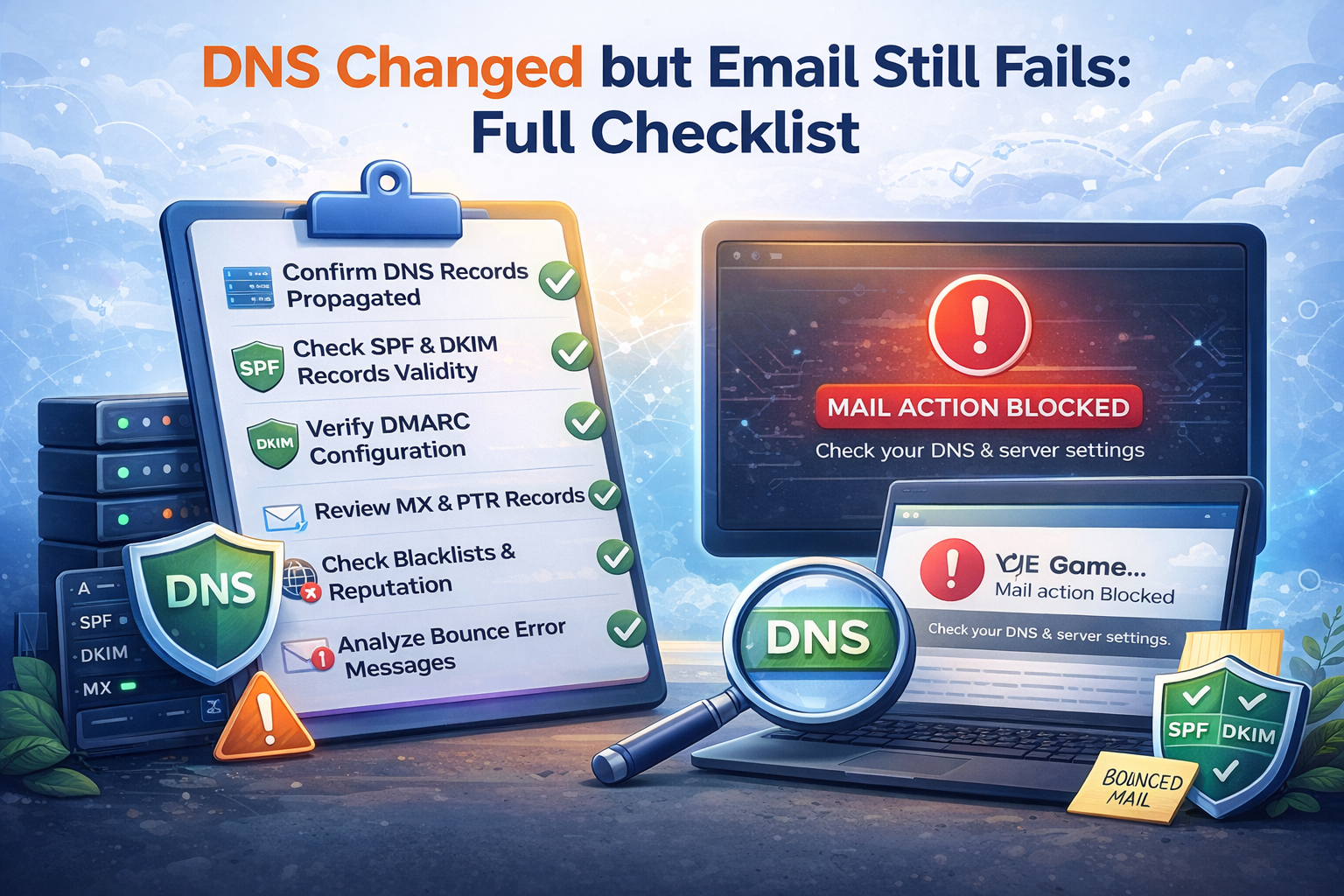
DNS Changed but Email Still Fails: Full Checklist
Updating MX, SPF, DKIM, or DMARC does not instantly fix mail delivery. This guide gives you a practical checklist for propagation, validation, reverse DNS, and blacklist checks after DNS changes.

How to Find the Right Abuse Contact for a Suspicious IP
When an IP address looks abusive, reporting it to the wrong place wastes time. This guide explains how to use WHOIS, ASN context, reverse DNS, and provider ownership to find the correct abuse contact.
Stay Updated on Network Security
Join our newsletter for the latest articles, tools, and best practices in network and system administration